Some of you folks might already know putty, the free SSH Client which we’ll use for toying around today showing you the reason why most companies do block SSH.
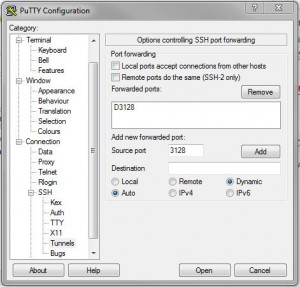
I assume you already know the basic settings – how to connect to a SSH server. If you browse through the settings you’ll find this page:
What we do here is something like a poor man’s ssh proxy: You ask PuTTy to open a connection and tunnel a port to a dynamic destination. I used port 3128 in our example which would be tunneled through our remote destination. Now any application that is able to use a socks proxy can connect through that port.
So if our firewall blocks i.e port 80 to prevent surfing, we could use Firefox’ feature to bypass that. As long as we can ssh to our target host which is able to use those specific ports, we successfully went around that blocker. As we use SSH, the connection itself is encrypted (but not DNS traffic!) which adds a little more security to it.
Tux2000 says:
1. Firefox und Thunderbird kann man so einstellen, dass auch DNS über Socks läuft (about:config -> network.proxy.socks_remote_dns), dann gibt es lokal keine verdächtigen DNS-Anfragen mehr.
2. PuTTY kann SSH auch durch einen HTTP-Proxy sprechen, der CONNECT unterstützt. Das sind praktisch alle, damit hinter dem Proxy HTTPS funktioniert. Kein CONNECT, kein HTTPS.
3. Damit man sich nicht auf jeden beliebigen Port CONNECTen kann, ist CONNECT in der Regel auf Port 443 beschränkt.
Abhilfe 1: sshd auf Port 443 laufen lassen und auf eine HTTPS-Webseite verzichten.
Abhilfe 2: Umschalter installieren, der aufgrund des unterschiedlichen Verhaltens von HTTPS und SSH den Port wahlweise auf den HTTPS-Server oder den sshd umschaltet. (z.B. http://xrunhprof.wordpress.com/2007/05/04/ssh-and-https-on-port-443-in-the-same-time/
Tux2000 <- nutzt all diese Features quasi täglich
Stargazer says:
Ich wollte erstmal einen Überblick geben, dass es möglich ist, aber es ist immer wieder erfrischend zu hören, dass ich nicht der Einzige bin, der solche Aktionen fährt.
Stef says:
Ihr seid aber nur vieleicht Spiesser. Echte Sadisten tunneln via Nameserver requests :P